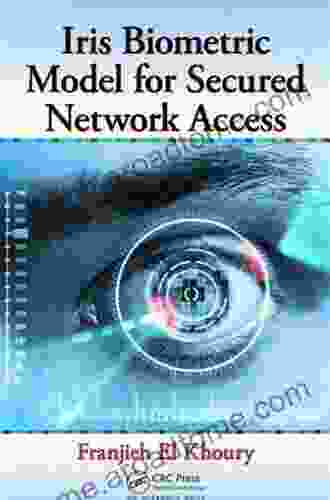
Iris Biometric Model for Secured Network Access

In today's digital landscape, network security is paramount. With the surge in cyber threats and data breaches, organizations are constantly seeking innovative and robust ways to protect their networks and sensitive information. Among the latest advancements in security technology, the iris biometric model has emerged as a game-changer.
5 out of 5
| Language | : | English |
| File size | : | 13667 KB |
| Print length | : | 220 pages |
The Unique Iris: A Natural Identifier
The iris, the colored part of the eye, contains complex and intricate patterns that are unique to each individual. These patterns remain stable throughout a person's life, making the iris an ideal biometric identifier. Unlike other biometric traits, such as fingerprints or facial features, the iris is less susceptible to forgery or spoofing.
Iris Biometric Model: Principles and Operation
The iris biometric model leverages advanced image processing techniques to capture and analyze the unique patterns of the iris. It involves the following steps:
- Image Acquisition: A specialized camera captures a high-resolution image of the iris.
- Segmentation: The image is processed to isolate the iris from other parts of the eye.
- Normalization: The isolated iris is normalized to reduce variations in size, shape, and illumination.
- Feature Extraction: Advanced algorithms extract specific features from the iris, such as ridges, furrows, and crypts.
- Biometric Template Creation: The extracted features are combined to create a unique biometric template, which represents the individual's iris pattern.
Advantages of Iris Biometric Model
The iris biometric model offers numerous advantages over traditional security measures:
- High Accuracy: Iris recognition boasts an exceptionally low false acceptance rate, making it highly reliable for authentication purposes.
- Uniqueness: As mentioned earlier, iris patterns are unique to each individual, providing a strong basis for identity verification.
- Liveness Detection: Iris recognition systems typically incorporate liveness detection mechanisms, making it difficult for attackers to spoof or present fake iris images.
- Non-Invasive and Convenient: Unlike other biometrics, such as DNA or fingerprint scanning, iris recognition is non-invasive and requires minimal user interaction.
Applications of Iris Biometric Model in Network Security
The iris biometric model finds versatile applications in securing network access, including:
- Access Control: Organizations can replace or enhance existing access control mechanisms, such as passwords or keycards, with iris recognition to prevent unauthorized access to networks, buildings, or restricted areas.
- Two-Factor Authentication: Iris recognition can be integrated with other authentication methods, such as PINs or OTPs, to create a robust two-factor authentication system, reducing the risk of unauthorized access.
- Network Authentication: Iris recognition can be deployed for remote network authentication, enabling secure access to business applications, cloud services, and virtual private networks (VPNs).
The Future of Iris Biometric Model
The iris biometric model is still evolving, with ongoing research and development efforts to enhance its accuracy, efficiency, and scalability. Advancements in artificial intelligence (AI) and computer vision are expected to further improve the performance and applicability of iris recognition systems.
The iris biometric model represents a significant paradigm shift in network security. Its unique advantages, including high accuracy, uniqueness, and liveness detection, make it an ideal solution for securing network access and protecting sensitive information. As technology continues to advance, we can expect the iris biometric model to play an increasingly prominent role in safeguarding our digital infrastructure and ensuring the privacy and integrity of our data.
5 out of 5
| Language | : | English |
| File size | : | 13667 KB |
| Print length | : | 220 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia John Baskin
John Baskin Bassel Elkadi
Bassel Elkadi Barbara Pleasant
Barbara Pleasant B J Schneider
B J Schneider Benjamin Kramer
Benjamin Kramer M J Gallagher
M J Gallagher Cynthia A Brandimarte
Cynthia A Brandimarte Bernard F Morrey
Bernard F Morrey Ben Rogers
Ben Rogers Bernadette Rodebaugh
Bernadette Rodebaugh Dery Dyer
Dery Dyer Nikki Stafford
Nikki Stafford Melissa Mccloud
Melissa Mccloud P Jira
P Jira Bedford Palmer
Bedford Palmer Scott Walls
Scott Walls Bethany Olds
Bethany Olds L William Ross Child M L C
L William Ross Child M L C Karen A Dahlman
Karen A Dahlman Sheryl Nussbaum Beach
Sheryl Nussbaum Beach
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Brennan BlairElevate Your Software Security: A Comprehensive Guide to Secure Coding in C...
Brennan BlairElevate Your Software Security: A Comprehensive Guide to Secure Coding in C... Langston HughesFollow ·19.3k
Langston HughesFollow ·19.3k Bernard PowellFollow ·2.4k
Bernard PowellFollow ·2.4k Brody PowellFollow ·2.8k
Brody PowellFollow ·2.8k Eli BlairFollow ·17.6k
Eli BlairFollow ·17.6k Levi PowellFollow ·16k
Levi PowellFollow ·16k Cormac McCarthyFollow ·19k
Cormac McCarthyFollow ·19k John Dos PassosFollow ·15.5k
John Dos PassosFollow ·15.5k Mike HayesFollow ·15k
Mike HayesFollow ·15k
 Corey Hayes
Corey HayesEasy Delicious Recipes To Heal The Immune System And...
: The Cornerstone...
 Cody Russell
Cody RussellMastering Medical Terminology: A Comprehensive Guide for...
Navigating the...
 Ibrahim Blair
Ibrahim BlairBeat Cancer Symptoms: Your Essential Guide to Symptom...
Are you struggling with the debilitating...
 Finn Cox
Finn CoxHow to Be the Best at Work and Still Have Time to Play:...
Are you tired...
5 out of 5
| Language | : | English |
| File size | : | 13667 KB |
| Print length | : | 220 pages |